Full story
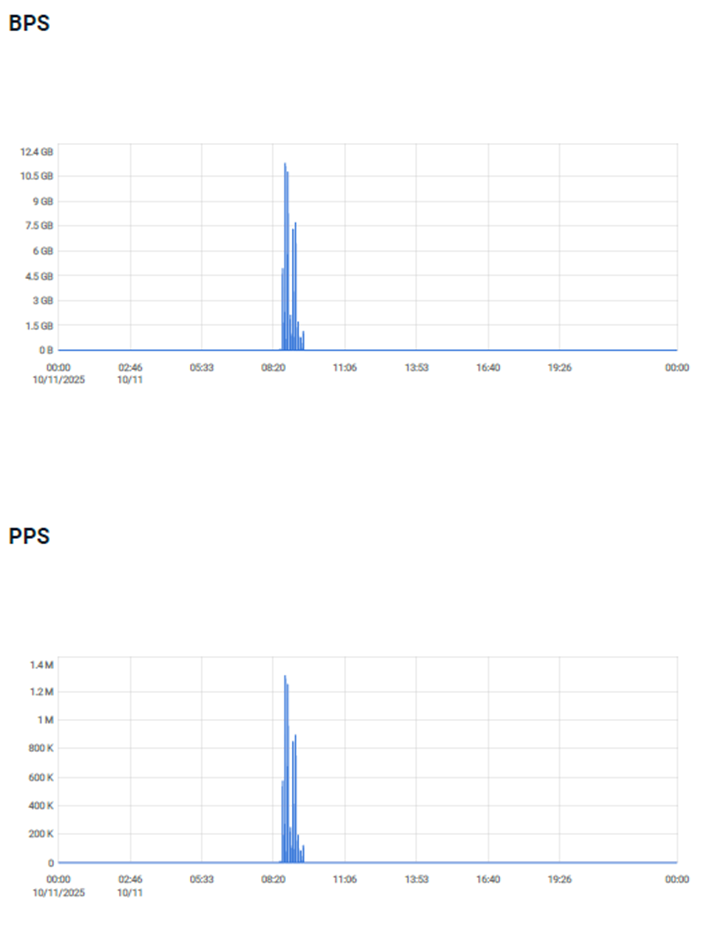
First attack - The first attack was held on November 10th, 2025, at about 8:30 am, and alerts began to be received regarding the detection of attacks on the Hosting customer’s IP addresses and the upstream ISP addresses.
The system identified an attack on about 500 IP addresses that included several vectors of attack, to 2 destination ports (0,443) with a capacity of 11.3 GB of traffic that was blocked by FlowSec’s system.
The attacks lasted for about 1 hour, while the Packet Per Second Traffic reached about 1.3M PPS.
The attack protocols were ICMP, UDP, and TCP (PSH, SYN, ACK) on the following ports: 0, 443.
The system detected the attack and created signatures that were sent to the Hosting and the ISP’s routers. During the detection of the attacks and the creation of signatures, email alerts were sent to the Hosting customer and their ISP for each signature.
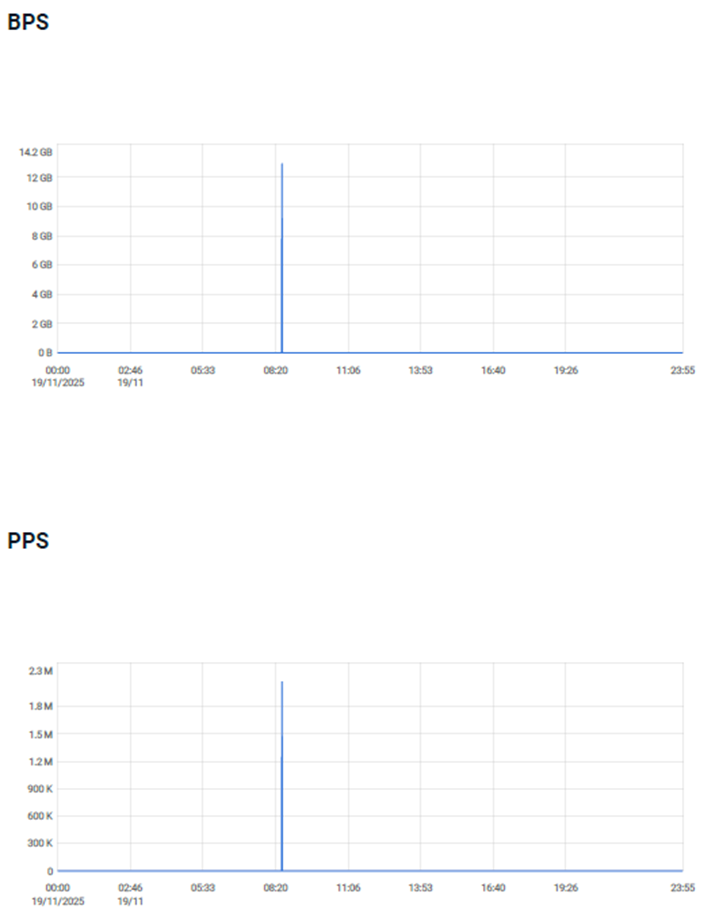
Second attack - The second attack was held on November 19th, 2025, at about 8:20 am, and alerts began to be received regarding the detection of attacks on the Hosting customer’s IP addresses.
The system identified an attack on two /25 subnets (2*128 IP addresses) that included one vector of attack with a capacity of 12.9 GB of traffic that was blocked by FlowSec’s system.
The attacks lasted for about 20 minutes, while the Packet Per Second Traffic reached about 2.1M PPS.
The attack protocols were ICMP, UDP, and TCP (PSH, SYN, ACK) on the following ports: 0, 443.
The system detected the attack and created signatures that were sent to the Hosting and the ISP’s routers. During the detection of the attacks and the creation of signatures, email alerts were sent to the Hosting customer and their ISP for each signature.
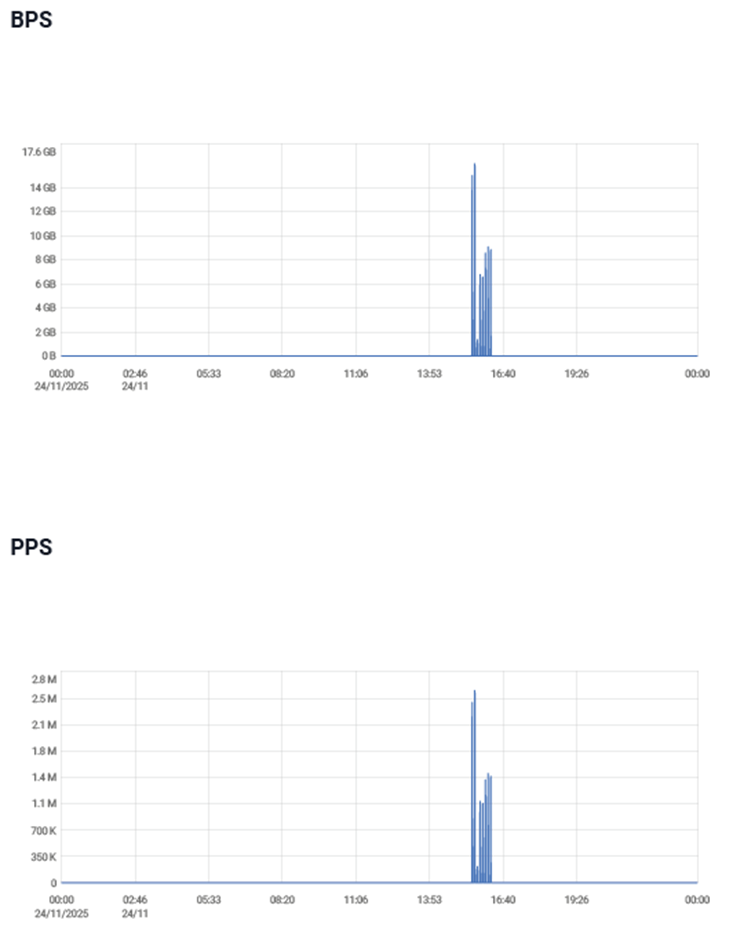
Third attack - The third attack was held on November 24th, 2025, at about 15:30, alerts began to be received regarding the detection of attacks on the Hosting customer’s IP addresses.
The system identified an attack on about 500 IP addresses that included several vectors of attack, to a destination port (53) with a capacity of 16 GB of traffic that was blocked by FlowSec’s system.
The attacks lasted for about 30 minutes, while the Packet Per Second Traffic reached about 2.6M PPS.
The attack protocols were UDP and GRE on port 53.
The system detected the attack and created signatures that were sent to the Hosting and the ISP’s routers. During the detection of the attacks and the creation of signatures, email alerts were sent to the Hosting customer and their ISP for each signature.
Loss prevention - Loss prevention for the hosting customer – the customer estimation for loss prevention is about $1.1M for the total 3 attacks.
First attack graph
Second attack graph
Third attack graph
Global Shield
To resolve the issue, FlowSec’s system sent the attack signatures to the routers of Hosting and the upstream ISP, which successfully blocked the malicious traffic and cleaned the pipe leading to the attacked Hosting customer.
At the end of the attacks and after the traffic returned to normal levels, the signatures were removed from the Hosting and ISP’s routers according to system settings.
During the attack, the customer was working as usual and serving its customers.





